In a nutshell: Safety researchers have found a brand new malware menace designed to abuse steganography methods. Worok seems to be a posh cyber-espionage operation whose particular person phases are nonetheless partially a thriller. The operation’s ultimate goal, nonetheless, has been confirmed by two safety companies.
Worok is utilizing multi-stage malware designed to steal information and compromise high-profile victims, utilizing steganography methods to cover items of the ultimate payload in a plain PNG picture file. The novel malware was first found by ESET in September.
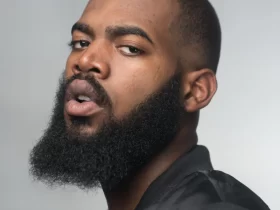
The corporate describes Worok as a brand new cyber espionage group that’s utilizing undocumented instruments, together with a steganography routine designed to extract a malicious payload from a plain PNG picture file. A duplicate of stated picture is proven under.
The Worok operators had been focusing on high-profile victims like authorities companies, with a selected give attention to the Center East, Southeast Asia and South Africa. ESET’s information into the menace’s assault chain was restricted, however a brand new evaluation from Avast is now offering further particulars about this operation.

Avast suggests Worok makes use of a posh multistage design to cover its actions. The strategy used to breach networks continues to be unknown; as soon as deployed, the primary stage abuses DLL sideloading to execute the CLRLoader malware in reminiscence. The CLRLoader module is then used to execute the second-stage DLL module (PNGLoader), which extracts particular bytes hidden inside PNG picture information. These bytes are used to assemble two executable information.
The steganography method utilized by Worok is called least vital bit encoding, which hides small parts of the malicious code within the “lowest bits” inside particular pixels within the picture that may be recovered later.
The primary payload hidden with this technique is a PowerShell script for which neither ESET nor Avast have been in a position to acquire a pattern but. The second payload is a customized information-stealing and backdoor module named DropBoxControl, a routine written in .NET C#, designed to obtain distant instructions from a compromised Dropbox account.
DropBoxControl can execute many – and probably harmful – actions, together with the power to run the “cmd /c” command with given parameters, launch executable binary information, obtain information from Dropbox to the contaminated (Home windows) gadget, delete information on the system, exfiltrate system data or information from a selected listing, and extra.
Whereas analysts are nonetheless placing all of the items collectively, the Avast investigation confirms that Worok is a customized operation designed to steal information, spy, and compromise high-level victims in particular areas of the world.